If you were convinced you knew the way home, would you still turn on your…
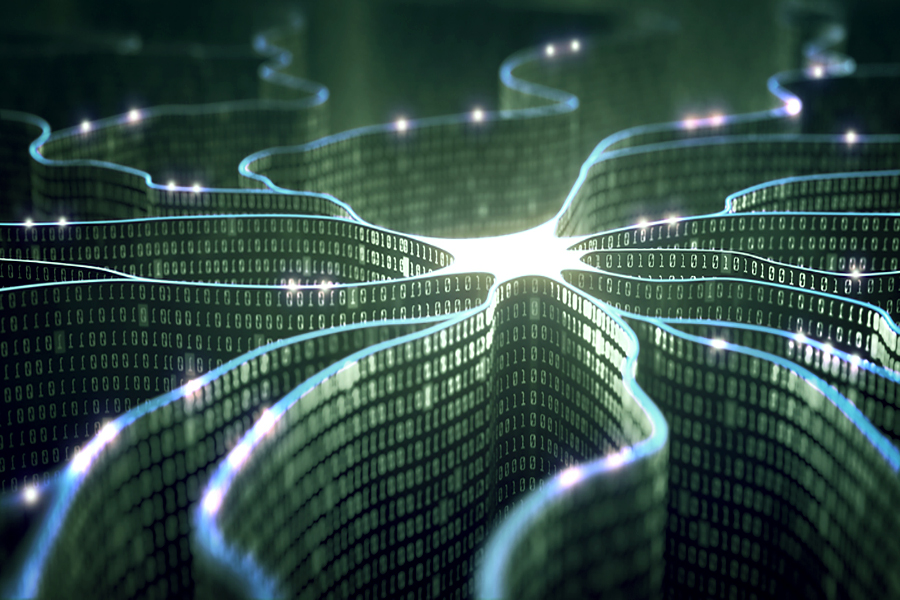
A new breed of algorithms has mastered Atari video games 10 times faster than state-of-the-art…
Despite being the most advanced quantum technology, secure encryption of information units based on a…
The most basic type of quantum information processing is quantum entanglement. In a new study…
With almost every online purchase, a person’s personal information — name, date of birth and…
HBO’s popular television series “Game of Thrones” returns in April, but millions of fans continue…
A novel model developed by MIT and Microsoft researchers identifies instances in which autonomous systems…
More organizations than ever are conducting business online. An expanding digital footprint and increasingly sophisticated…
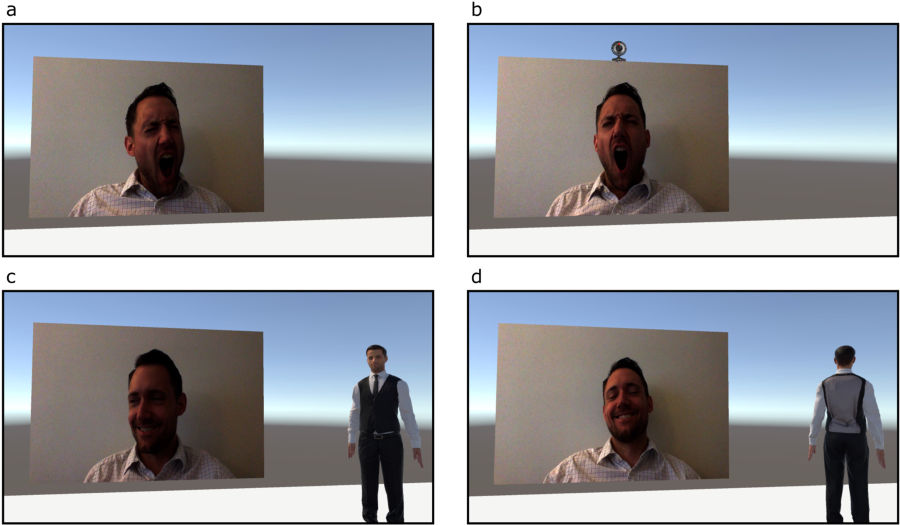
Immersive virtual reality (VR) can be remarkably lifelike, but new University of British Columbia (UBC)…
“Happier Classrooms: the simple way to build an amazing classroom community.” So reads the message…