Organizations working to meaningfully improve diversity and inclusion in STEM may be missing a crucial…
Austin Moody wanted to apply his cybersecurity skills in his home state of Michigan, teaming…
NEXT month the University of Huddersfield is to deliver an Artificial Intelligence Skills Bootcamp that will connect people…
Researchers from North Carolina State University have developed a software toolkit that allows users to…
Apple released a critical software patch to fix a security vulnerability that researchers said could…
Risk managers in South Africa must suffer perpetual headaches these days. There is a crammed…
Researchers from the Singapore University of Technology and Design (SUTD) released 16 new security vulnerabilities,…
A rude awakening came to thousands of Americans in early May. Many motorists who had…
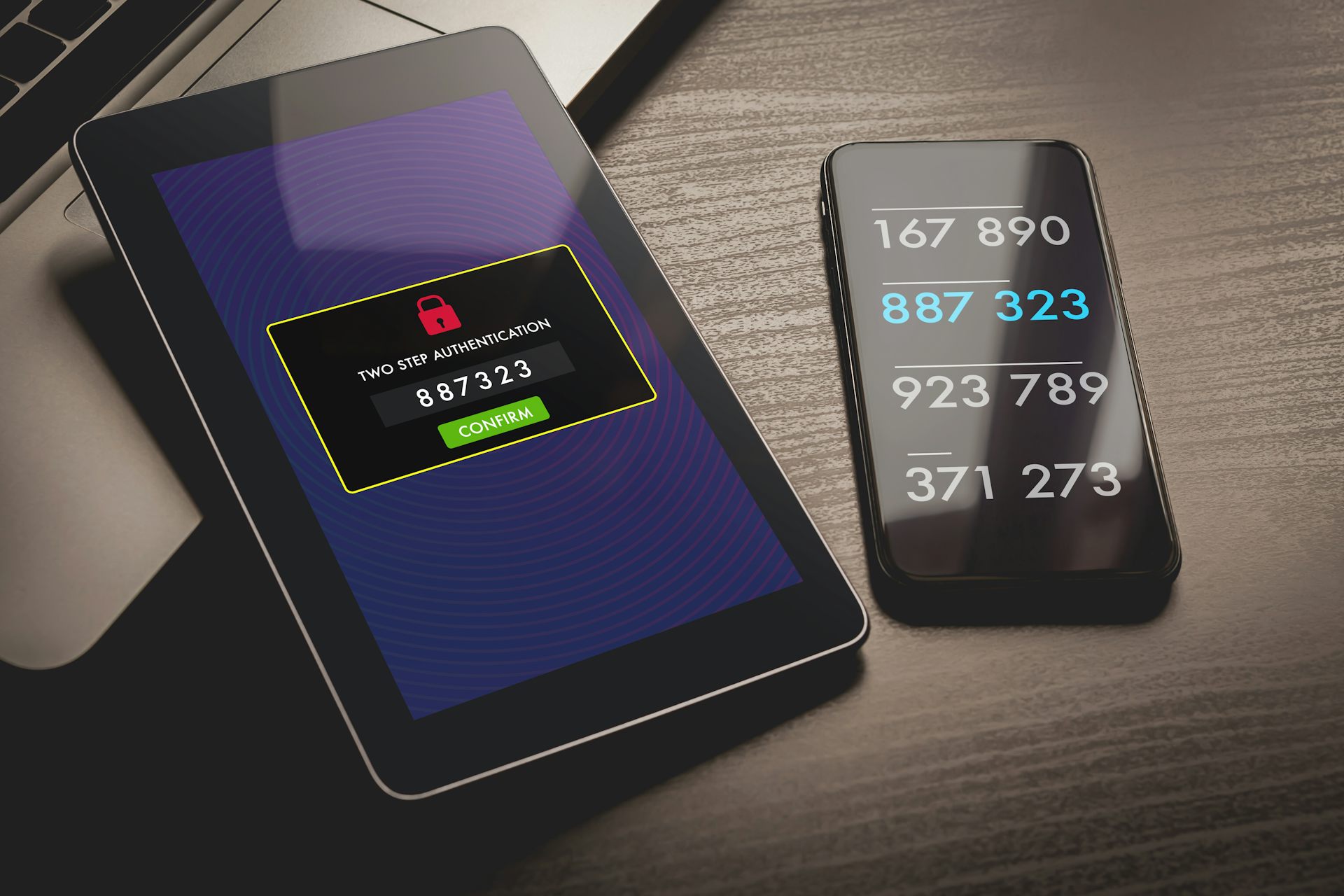
It’s now well known that usernames and passwords aren’t enough to securely access online services.…
What do cyberspace and outer space have in common? As we make clear in a…