Each year, Marine Corps Systems Command acquires a range of ground-based innovations designed to meet…
In a Policy Forum, Alessandro Acquisti and colleagues argue that the evolutionary roots of human…
The MITRE-Harris Poll Survey on innovation found U.S. residents are broadly concerned about the nation’s…
While cybercrime gets a lot of attention from law enforcement and the media these days,…
Researchers have found a way to make AI-generated voices, such as digital personal assistants, more…
Consumers and employees will be watching closely in 2022 to ensure that multinational corporations are…
Computer systems that are physically isolated from the outside world (air-gapped) can still be attacked.…
The University of Texas at El Paso will enhance the capacity of the regional and…
The resilience of America’s critical infrastructure networks has been tested over the last year by…
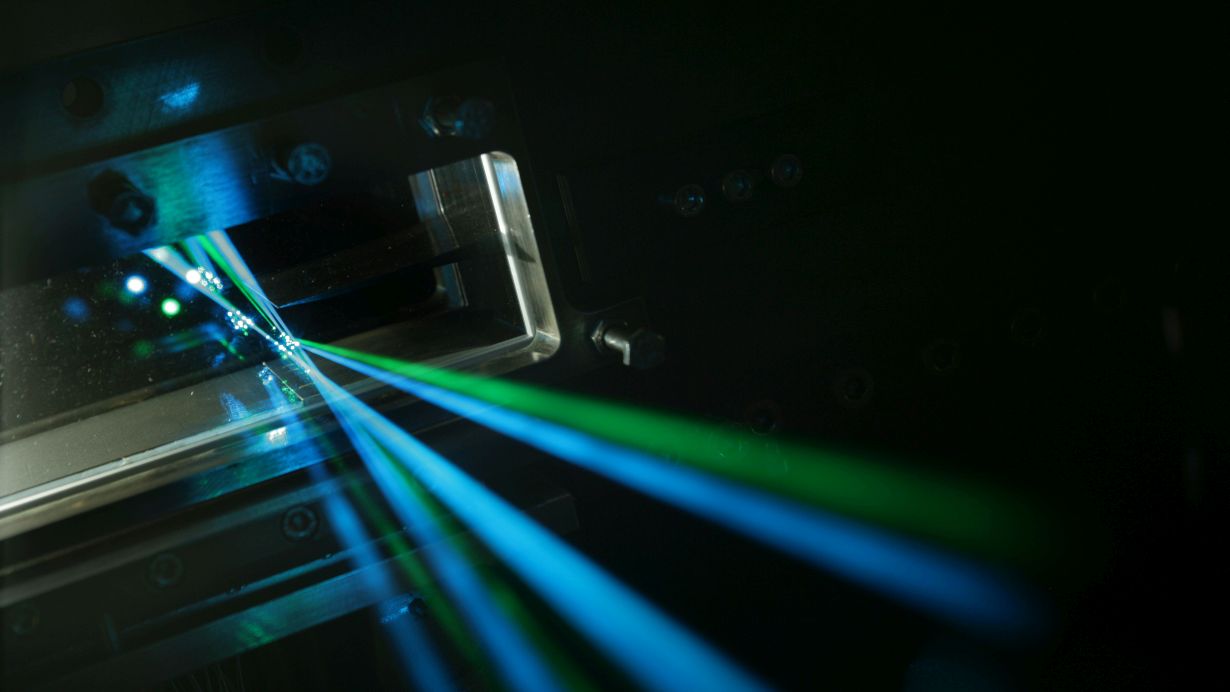
The Naval Postgraduate School (NPS) has added a new capability to the university’s technological toolbelt…