Singapore’s Quantum Engineering Programme (QEP) will start conducting nationwide trials of quantum-safe communication technologies that…
The time a person spends on different smartphone apps is enough to identify them from…
A heart attack patient, recently discharged from the hospital, is using a smartwatch to help…
Researchers at Rutgers University-New Brunswick have published “Face-Mic,” the first work examining how voice command features on…
At a U.S. Army base command center, a computer beeps and displays a warning: the…
The Apple AirTag, the newest addition to the Apple family, launched last year and is…
Over the last 50 years, the computer has been transformed from a hulking scientific super-tool…
For teachers at a middle school in New Mexico’s largest city, the first inkling of…
On Jan. 14, 2022, the FSB, Russia’s domestic intelligence service, announced that it had broken…
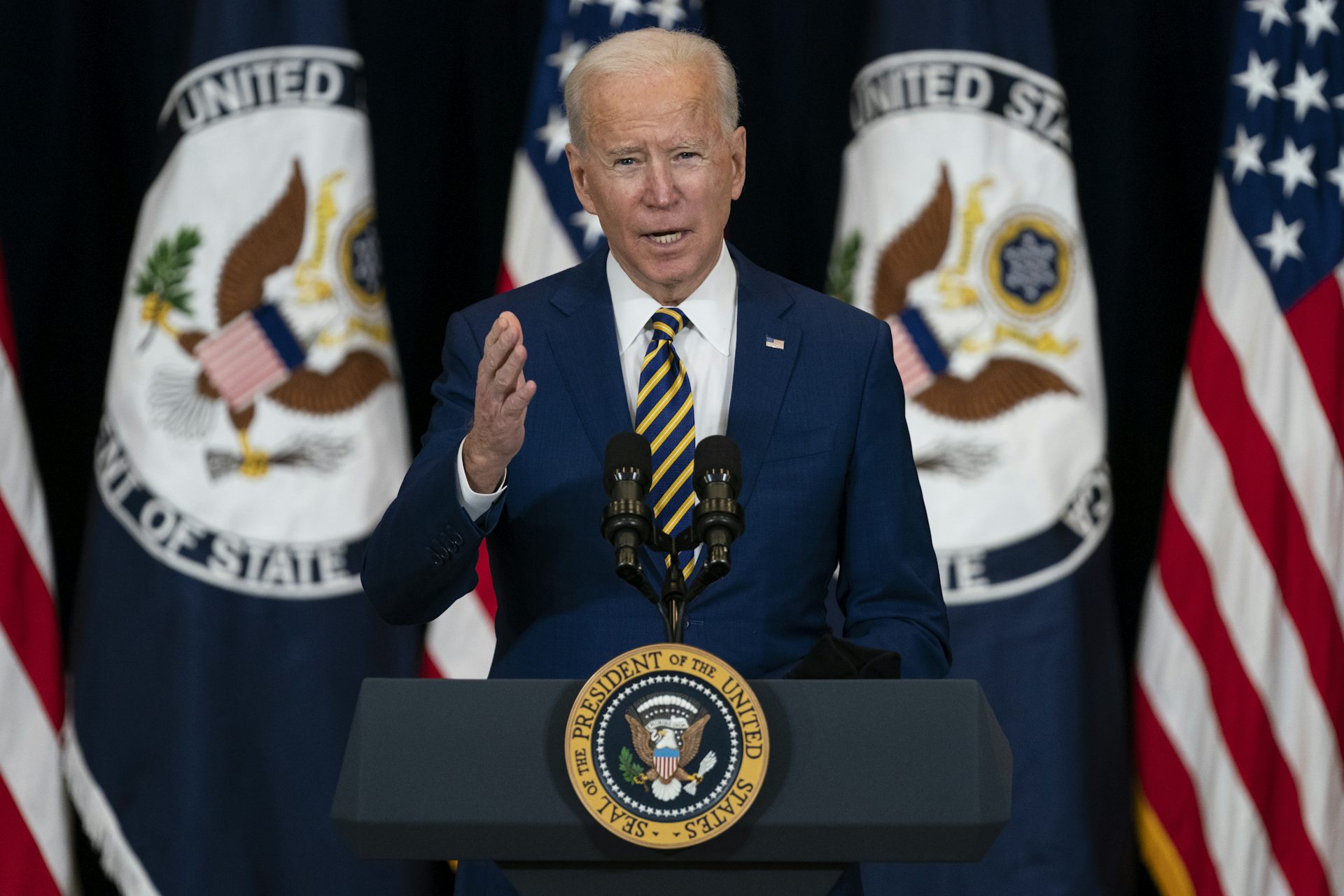
As tensions mount between Russia and the West over Ukraine, the threat of Russian cyberattacks…