A team at Los Alamos National Laboratory has developed a novel approach for comparing neural networks that…
To help meet the growing demand for cybersecurity experts, the National Science Foundation’s CyberCorps Scholarship…
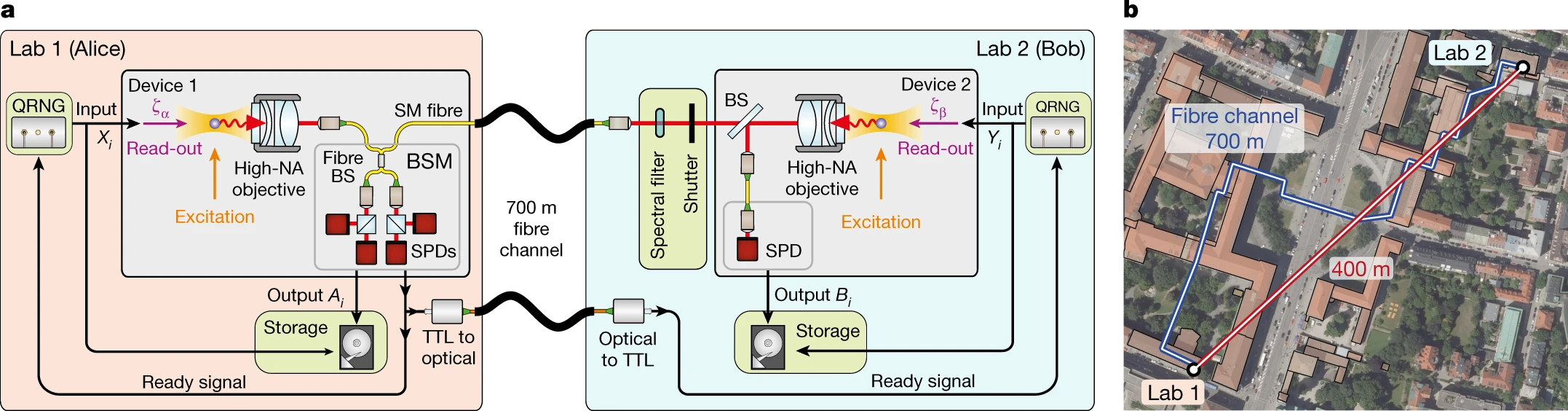
Researchers at Cornell University have developed a mechanism for preserving anonymity in encrypted messaging –…
Training a machine-learning model to effectively perform a task, such as image classification, involves showing…
Data privacy in the U.S. is, in many ways, a legal void. While there are…
A former head of security at Twitter has filed whistleblower complaints with U.S. officials, alleging…
Using a $7.5 million grant from the National Science Foundation (NSF), University of Florida engineers…
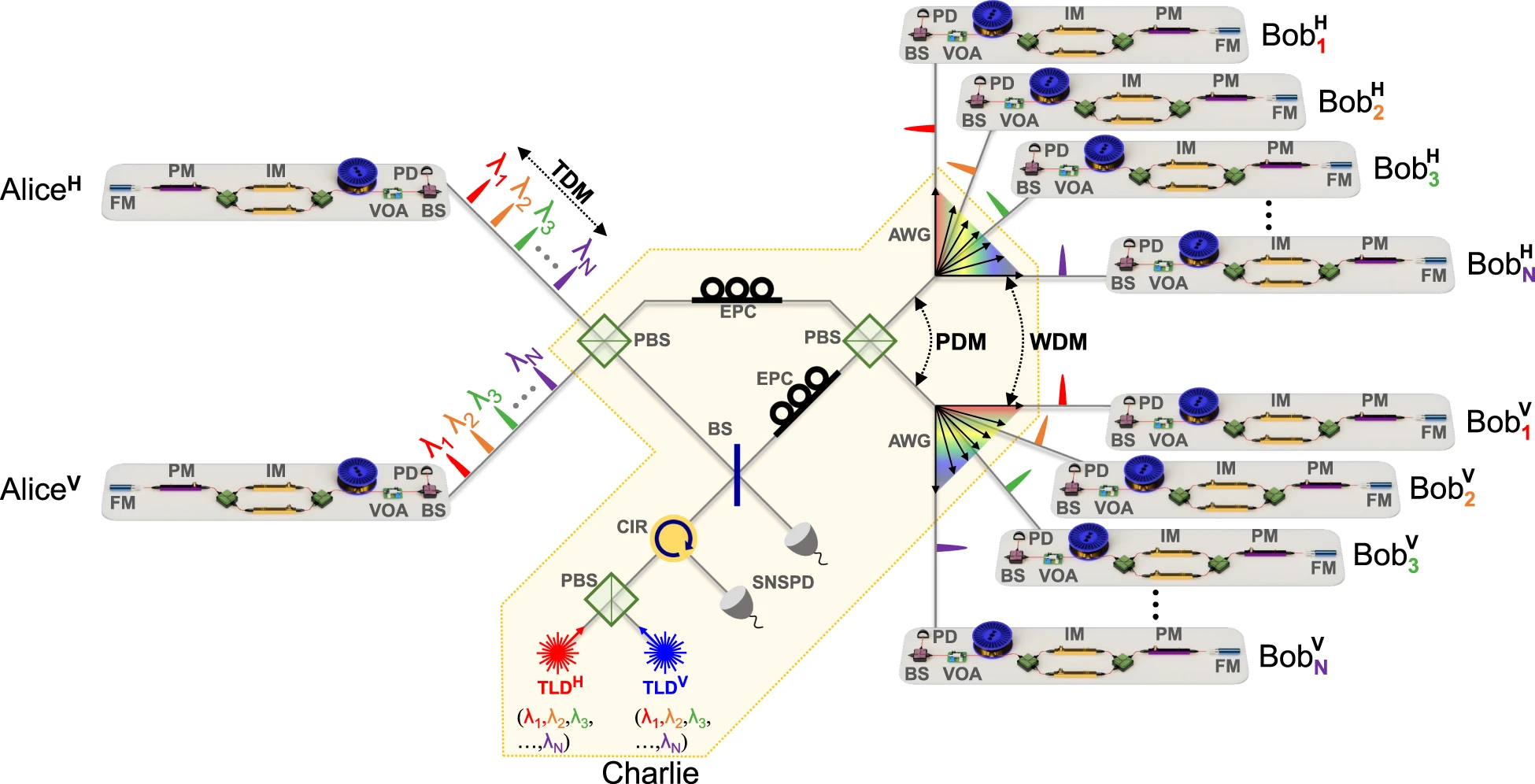
The Internet is teeming with highly sensitive information. Sophisticated encryption techniques generally ensure that such…
In modern cryptosystems, users generate public and private keys that guarantee security based on computational…
The New York University Tandon School of Engineering is launching its inaugural Chief Information Officer (CIO) Program to provide senior…