Smartphone spyware apps that allow people to spy on each other are not only hard…
The National Cybersecurity Center (NCC) announced Wednesday the addition of three new esteemed board members, adding to…
Sertainty has published a new whitepaper titled Quantum Computer Threats Against PKI Data Security and a Digital-ID Based…
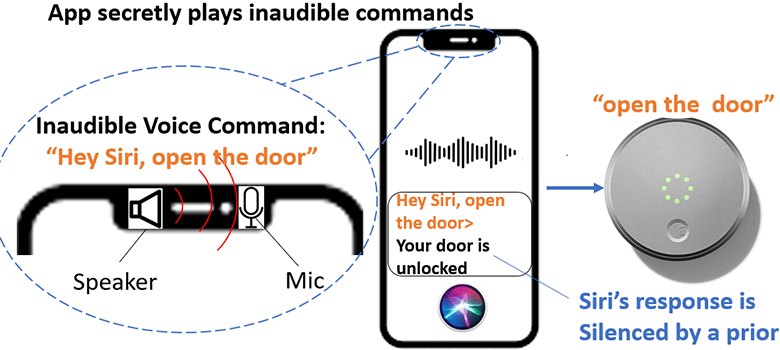
Guenevere Chen, an associate professor in the UTSA Department of Electrical and Computer Engineering, recently…
Smartphone spyware apps that allow people to spy on each other are not only hard…
Only a small percentage of the 500 most visited websites in Spain (which include everything…
Britain’s security minister said Tuesday he has asked the country’s National Cyber Security Center to…
A ransomware cyberattack on one of Barcelona’ s main hospitals has crippled the center’s computer…
An ambitious and wide-ranging White House cybersecurity plan released Thursday calls for bolstering protections on critical sectors…
A cybersecurity technique that shuffles network addresses like a blackjack dealer shuffles playing cards could…