The undersea cable system faces threats from deep-sea mining, geopolitical sabotage, and AI-driven demand, requiring…
The Biden-era structure is vital to U.S. cybersecurity, but the Trump administration could take steps…
Precisely targeted cyber operations can remove blocking rules or disable network-blocking equipment. Cyberspace and the…
Vibe coding produces software riddled with insecurities. Will risk management and regulatory compliance, too, fall…
Holding AI developers responsible for any harm their systems cause may not be the most…
Criminals can use artificial intelligence, specifically large language models, to autonomously carry out ransomware attacks…
From airline tickets and e-commerce to rideshares and food delivery, some companies are quietly using…
A review of “Wrong: How Media, Politics, and Identity Drive Our Appetite for Misinformation” by…
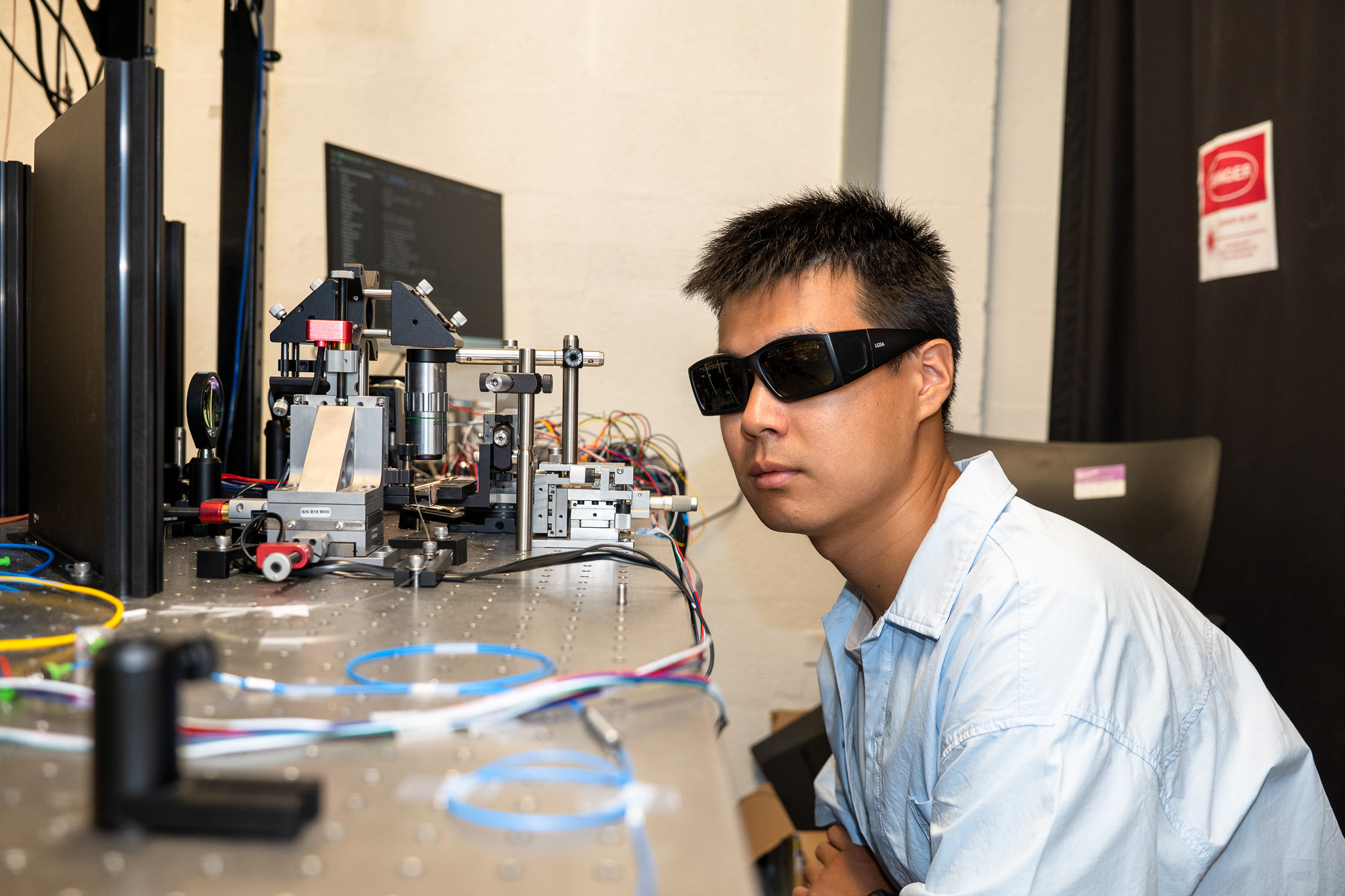
New integrated chip shows how quantum networks could “speak” today’s internet language on existing commercial…
Although some fear that AI will flood the market, harming existing copyrighted works, historical examples…




.jpeg?sfvrsn=d5075110_5)
.webp?sfvrsn=867f111c_4)