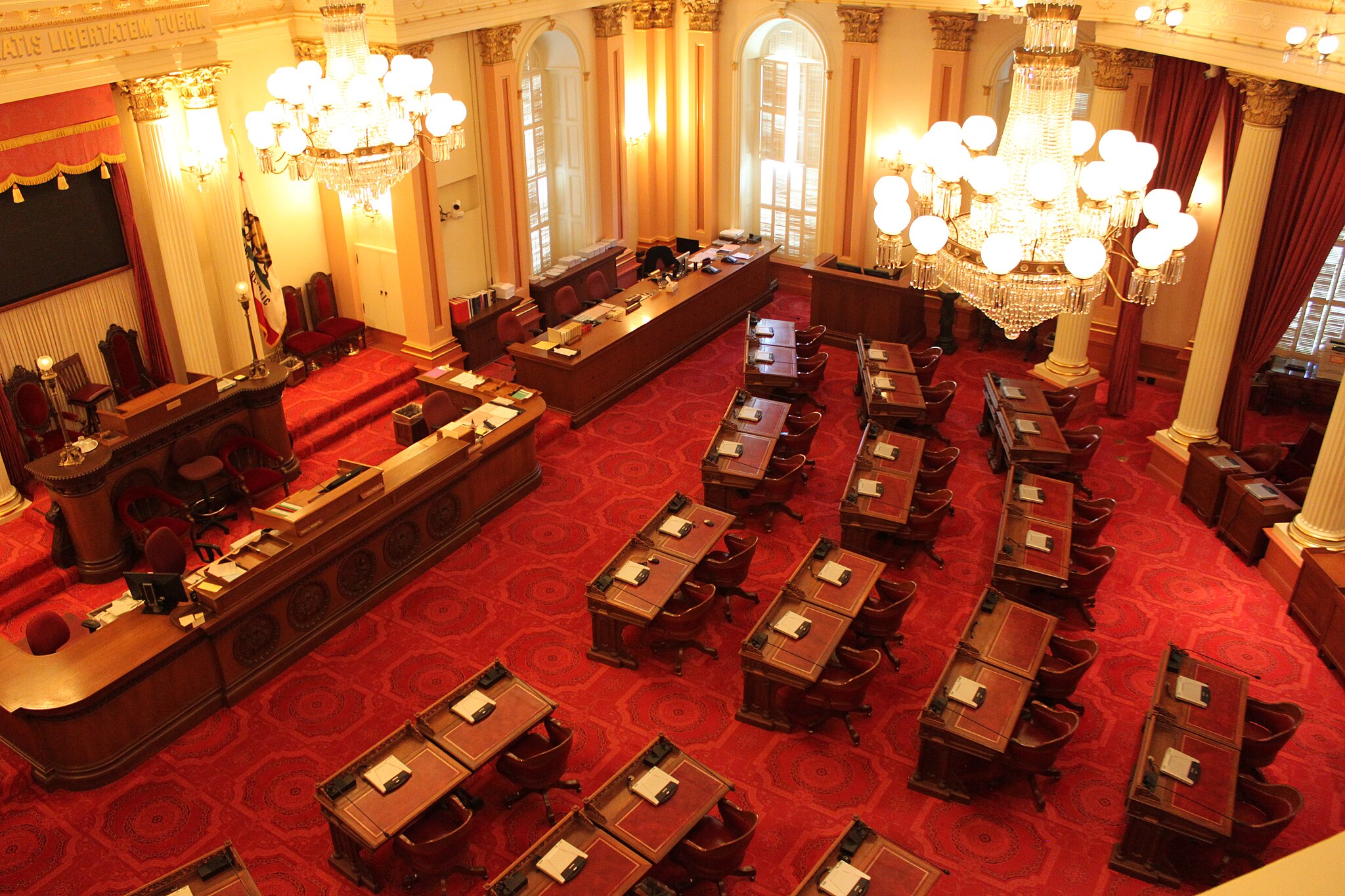
Regulation of AI models themselves should be done on the federal, not state, level. As…
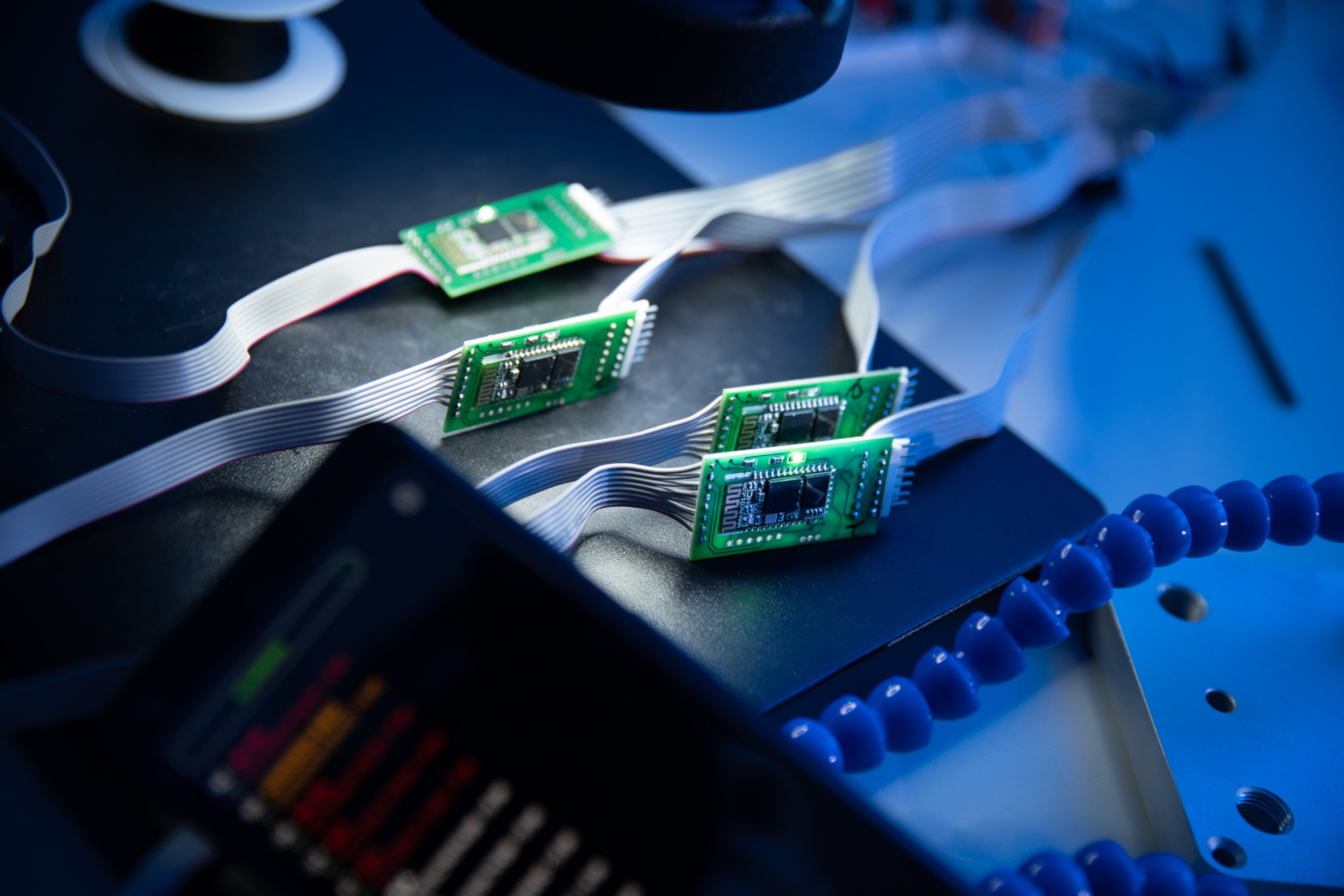
Sanctions could prove an effective tool in the fight against spyware abuses. Spyware is a…
Cyber operations reveal their limitations as means of warfare, but territorial conquest opens unique opportunities…
A useful lesson from the economic concept of the “least cost avoider,” suggests that significant…
Whatever their policy merits, safety limitations on AI development generally do not raise First Amendment…
Ironically, the two countries can look to the past, not the future, for inspiration on…
A review of Lennart Maschmeyer, “Subversion: From Covert Operations to Cyber Conflict” (Oxford University Press,…
Amid surging attacks, Kenya aims to expand its technology sector and improve cybersecurity to protect…
NATO allies need to allow their militaries to be proactive in cyberspace to ensure the…
Affected Platforms: Microsoft Windows Impacted Users: Microsoft Windows Impact: Compromised machines are under the control of the threat…