Large language models cannot eliminate the need for human judgment in constitutional law. Modern artificial…
The latest edition of the Seriously Risky Business cybersecurity newsletter, now on Lawfare. The U.S. government…
The U.S. has invited a conundrum for the Department of Justice upon itself. On Aug.…
The new UN cybercrime convention left everyone unhappy. But is that necessarily the sign of…
Teenagers use generative artificial intelligence for many purposes, including emotional support and social interactions. A study by…
The SEC’s cyber disclosure rule underscores the need for regulatory harmonization post-Loper Bright. CISA’s rules…
A news story used brokered location data to track military personnel—illuminating a considerable threat to…
The technique could make AI systems better at complex tasks that involve variability. Fields ranging…
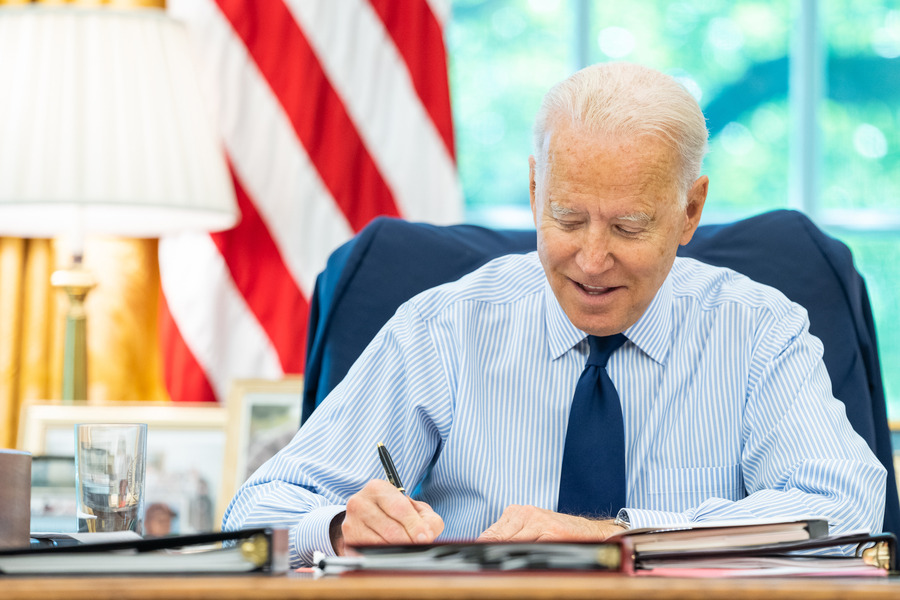
The memorandum provides guidance to government agencies—in coordination with the private sector—for responsible AI development. …
Law enforcement and national security officials have fought end-to-end encryption for decades—but the technology is…




.jpg?sfvrsn=cecda2d5_5)