What happens if Trump deploys cyber forces in the U.S.? Cyber operations may already be…
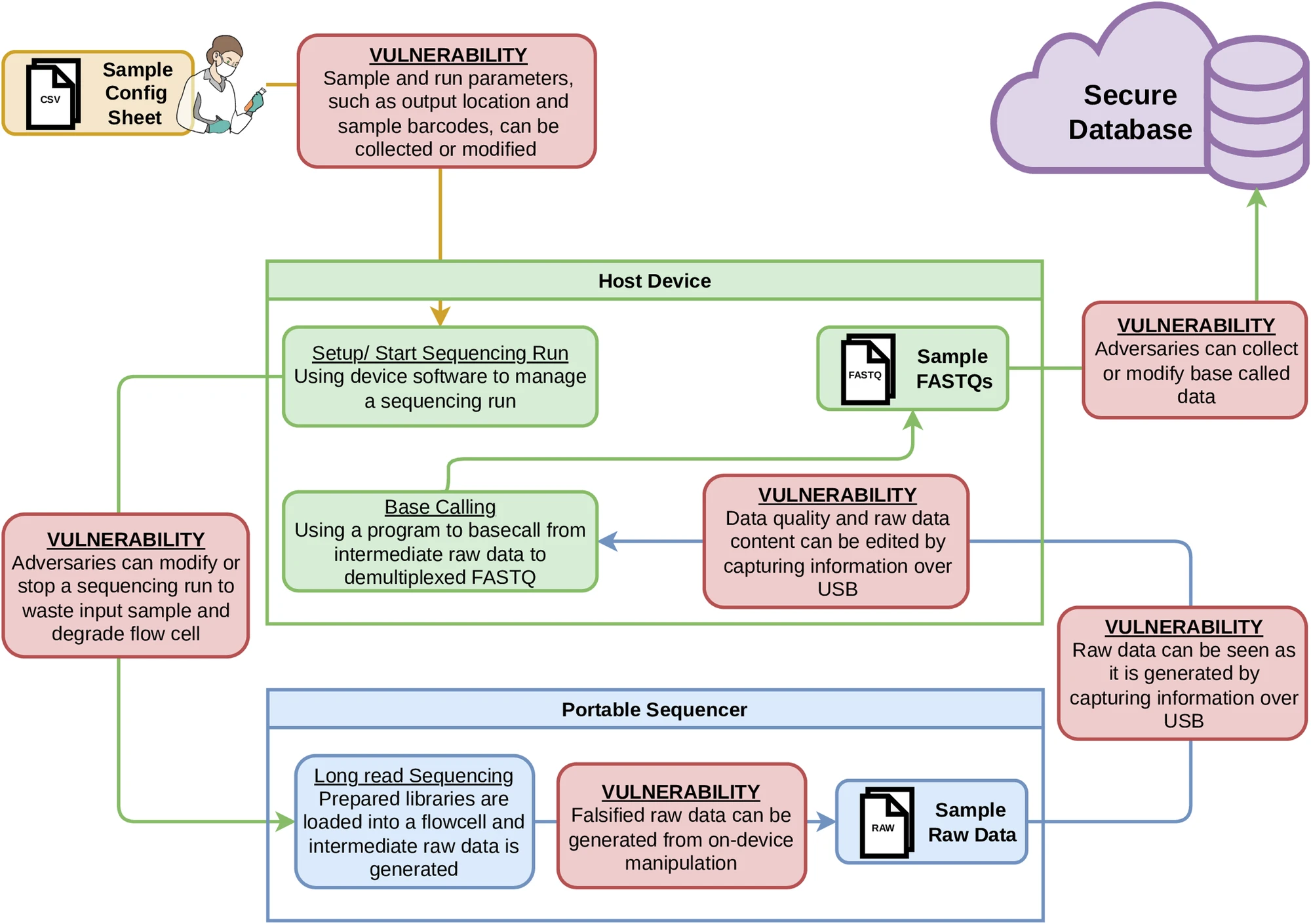
Portable genetic sequencers used around the world to sequence DNA have critical, previously unreported security…
Study shows short-term increase in student trust for generative AI programming tools; long-term trust still…
Ukraine’s offensive cyber strategy demonstrates that Western governments need to adopt a “responsibly irresponsible” warfighting…
The convention, which just opened for signature, is substantively similar to the Budapest Convention, but…
The AI race isn’t only about chips or tariffs. It’s also about who writes the…
Persistent penetration of domestic networks makes coordinated defenses and robust deterrence essential to preventing cyber…
To promote AI accountability and peer-monitoring, AI firms should be held collectively liable for catastrophic…
As geopolitical tensions rise, cyber attacks are intensifying, with public services increasingly targeted. Over 130 countries have experienced…
Microsoft’s recent action against Israel’s Unit 8200 demonstrates Big Tech’s growing ability to limit state-operated…



.jpg?sfvrsn=d7b2f221_5)


.jpg?sfvrsn=f727de95_5)

.jpg?sfvrsn=d5e57b75_7)