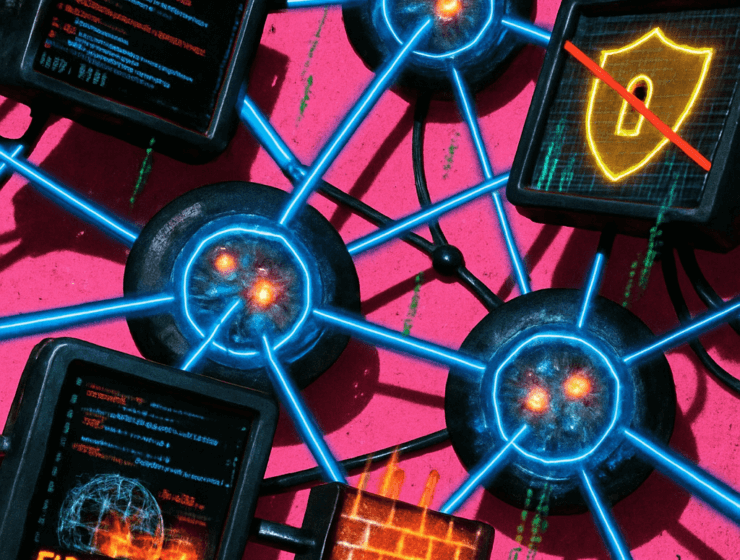
Introduction Cyber power is increasingly defined by persistence rather than destructive capability. State-aligned threat actors…
STRATEGY & THREATS
Introduction Cybersecurity risk was once framed around preventing breaches and minimizing isolated incidents. Today, organizations…
Introduction Cyber conflict has moved away from isolated attacks toward persistent campaigns designed to shape…
Introduction Cyber conflict is no longer episodic. Instead, it has become a continuous feature of…
Introduction The conflict in Ukraine has reshaped assumptions about the decisive role of offensive cyber…
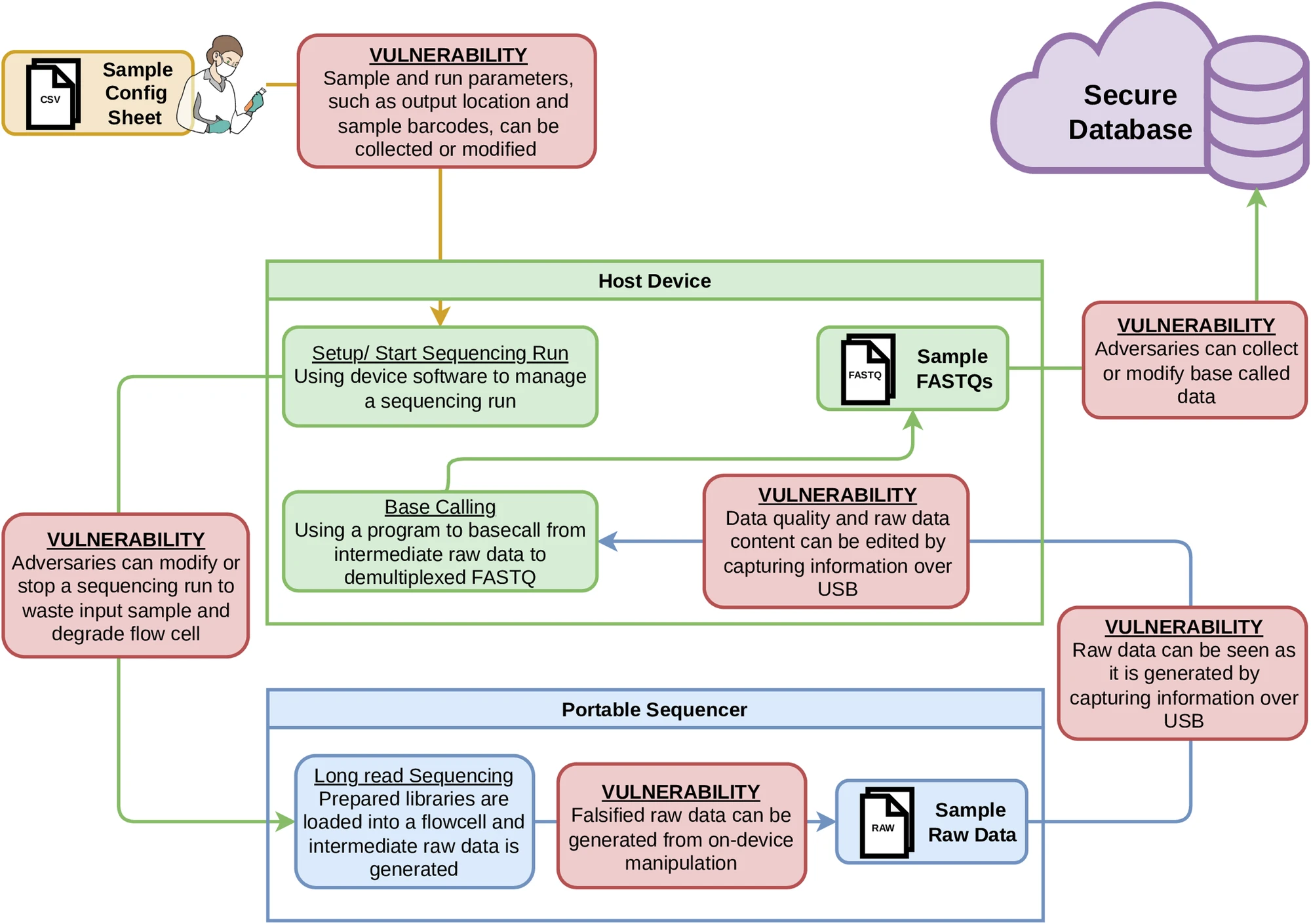
Portable genetic sequencers used around the world to sequence DNA have critical, previously unreported security…
Ukraine’s offensive cyber strategy demonstrates that Western governments need to adopt a “responsibly irresponsible” warfighting…
Persistent penetration of domestic networks makes coordinated defenses and robust deterrence essential to preventing cyber…
A major Japanese beverage producer says it has been hit by a cyberattack that left…
Authoritarian threats, coupled with ongoing corporate surveillance, demand that we rethink how we use digital…





.jpeg?sfvrsn=f8ab7a0d_5)